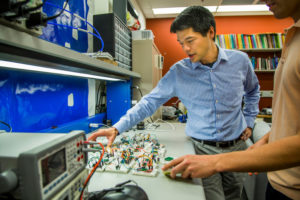
Kevin Fu, University of Michigan
The New York Times recently released an article called It’s Possible to Hack a Phone With Sound Waves, Researchers Show, which highlights CCC Council Member Kevin Fu’s work on embedded computer systems. Kevin and his team at the University of Michigan and collaborators at the University of South Carolina have found a vulnerability that allows them to take control of devices through the tiny accelerometers that are standard components in consumer products like smartphones, fitness monitors and even automobiles.
Accelerometers, which measure acceleration, are used for navigating, determining the orientation of a tablet computer, and measuring distance traveled in devices such as Fitbits. The research team used precisely tuned acoustic tones to deceive 15 different models of accelerometers into registering movement that never occurred. This approach served as a backdoor into the devices that enabled the researchers to control other aspects of the system.
From the University of Michigan press release:
The fundamental physics of the hardware allowed us to trick sensors into delivering a false reality to the microprocessor, Fu said.
Our findings upend widely held assumptions about the security of the underlying hardware. If you look through the lens of computer science, you won’t see this security problem. If you look through the lens of materials science, you won’t see this security problem. Only when looking through both lenses at the same time can one see these vulnerabilities.
The team tested 20 accelerometers from five different manufacturers. They were able to affect the information or output from 75 percent of the devices tests and were able to control the output in 65 percent of the devices.
The Department of Homeland Security has released a security advisory alert for chips produced by the semiconductor companies highlighted in this research.
To learn more and see videos of this research, please see this website. The paper also documents hardware and software changes manufacturers could make to protect against the flaws that the researchers discovered.